Expressvpn Glossary
Session hijacking
What is session hijacking?
Session hijacking is an attack in which an attacker takes control of an active, authenticated web session by obtaining a valid session identifier (session token). By stealing or predicting this identifier, the attacker can gain unauthorized access and act as the legitimate user in the application without obtaining the user’s credentials.
How does session hijacking work?
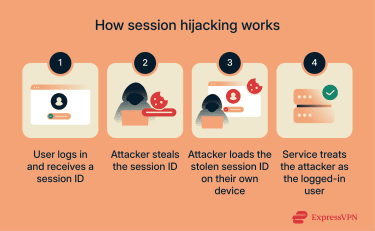
A typical session hijacking flow follows these steps:
- The user logs in: The user authenticates to the service. The service generates a session token (session ID) for that authenticated session and stores it on the client (commonly in a cookie).
- The attacker captures the valid session token: Through interception or theft (such as monitoring or intercepting unsecured network traffic, session sniffing, malware, injected scripts, or another method), the attacker obtains the active token associated with the victim’s authenticated session.
- The attacker injects or replays the token: The attacker places the stolen token into a browser, tool, or request stream so the service treats the attacker’s requests as part of the same authenticated session.
- The attacker gains access to the active session: If the token is accepted, the attacker can operate as the victim until the session expires, is terminated, or the identifier is rotated or refreshed.
Common types of session hijacking
These are common session hijacking variants seen in web applications:
- Man‑in‑the‑middle (MITM) attacks: On unencrypted HTTP, an attacker intercepts client-server traffic to capture session tokens in transit.
- Session sidejacking over unsecured Wi‑Fi: Passive network sniffing captures session identifiers on insecure wireless networks (only for HTTP, not HTTPS).
- Malware‑based token theft: Malware extracts session cookies or tokens from the browser, disk, or memory.
- Session fixation: The attacker visits the site first, and the site assigns them a random session cookie. The attacker then smuggles the cookie to the victim, allowing the victim to log into their own account under the same session. Afterward, the attacker reuses the cookie to access the victim’s authenticated session. Reputable sites usually prevent this by regenerating the session ID at login and invalidating the old one.
- Cross‑site scripting (XSS)–based hijacking: Malicious JavaScript on a vulnerable page can steal a session token and send it to the attacker, or, even if the cookie is HttpOnly and can’t be read, run attacker-chosen actions directly in the victim’s browser using the victim’s logged-in session. Best practices often prevent token theft, but not everyone uses them, so it’s less common but still possible.
Security and privacy risks
Session hijacking can affect confidentiality, integrity, and account-level trust, depending on what the compromised session is permitted to do.
- Unauthorized account access: Attackers can access user accounts or internal systems associated with the compromised session.
- Data theft or alteration: Sensitive information can be viewed, copied, or modified within the session.
- Fraudulent transactions: Financial or account actions can be performed without authorization, where the session allows it.
- Public Wi‑Fi exposure: Session tokens can be exposed on insecure networks when traffic is not protected.
- Increased exposure to phishing and credential attacks: Compromised accounts can be used to impersonate the victim, distribute phishing messages, or capture additional credentials.
Further reading:
- How to hide your IP address and protect your online privacy
- What is data privacy and why it matters: A complete guide
FAQ
What can attackers do with a stolen session token?
Is session hijacking the same as an MITM attack?
Can session hijacking happen on HTTPS websites?
How do I know if my session was hijacked?
Does a virtual private network (VPN) help prevent session hijacking?
How can I prevent session hijacking?
Avoiding logins on unsecured public networks reduces interception risk, and a VPN can add protection on untrusted networks by encrypting traffic.
