Expressvpn Glossary
Data masking
What is data masking?
Data masking is a data protection technique that replaces sensitive information with modified or fictitious values. The masked data retains the original format and structure but no longer reveals the real underlying information.
How does data masking work?
Data masking works by transforming sensitive fields according to predefined rules. The process begins by identifying which fields contain sensitive information. Predefined masking rules are then applied to those fields, replacing real values with masked ones while preserving the original format and structure.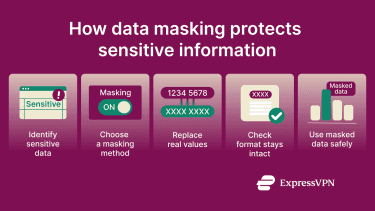
Why is data masking important?
Data masking is important because it allows organizations to use realistic data for testing, analytics, or training without exposing the original sensitive values. It also helps organizations meet privacy and data protection requirements such as the General Data Protection Regulation (GDPR) and Health Insurance Portability and Accountability Act (HIPAA), as it limits how often real data is accessed or shared.
Data masking methods
Here are some common ways sensitive data is altered or hidden:
- Tokenization: Replaces sensitive data with placeholders called tokens. The original data is stored separately and can only be accessed through controlled systems.
- Shuffling: Rearranges values within a dataset so they no longer match the original records. This keeps the data realistic while breaking direct links to real people or accounts.
- Hashing: Scrambles data so it can’t be read or reversed, which makes it useful for protecting passwords and similar data.
- Encryption: Transforms data into unreadable text using a cryptographic key. With the correct key, the original data can be restored. Unlike hashing, encryption can be reversed.
- Nulling: Removes sensitive data by replacing it with empty or null values. This prevents exposure but can reduce how useful the data is.
Types of data masking
While masking methods describe how data values are altered, masking types describe when and how those methods are applied:
- Static data masking: Permanently replaces sensitive data before it’s used or shared.
- Dynamic data masking: Hides sensitive information when it’s viewed, so different people see different versions of the same data depending on what they’re allowed to access.
- Deterministic masking: Always replaces the same original value with the same masked value.
- On-the-fly masking: Hides sensitive data as it’s viewed or shared, without changing the original stored data.
- Redaction: Hides or removes sensitive information entirely by masking characters or replacing values with nulls.
Data masking tools
Here are commonly used tools that apply data masking methods and types across databases and data pipelines in real environments:
- IBM InfoSphere Optim Data Privacy: Masks sensitive data in non-production environments such as development and testing. It applies masking rules across databases while keeping data consistent for analysis and system testing.
- AWS Database Migration Service masking transformations: Applies masking rules to selected database columns during data migration or replication. Supported options include digit masking, randomization, and hashing.
- Oracle Data Masking and Subsetting: A database-level tool that masks sensitive fields and creates reduced, masked copies of production data for development, testing, or analytics.
Further reading
- What is data anonymization?
- How to hide your IP address and protect your online privacy
- What is email masking?
- What are anonymous proxies, and how do they work?
- What is data privacy and why does it matter?
