What can someone do with my email address without a password?
An email address can reveal more than most people realize. In the wrong hands, it could help locate social media profiles, build a personal profile for targeted attacks, or launch phishing and spam campaigns.
This guide covers the main risks of someone knowing your email address and the steps to protect your personal data.
How do hackers get email addresses?

Cybercriminals can obtain email addresses through both legitimate and illicit methods. These include:
- Data leaks and breaches: Hackers break into company databases to steal entire lists of email addresses, which they then use directly for attacks or sell on dark web marketplaces.
- Phishing: Criminals create fake websites or sign-up forms, promising interesting newsletters or exclusive discounts for anyone who enters their email address.
- Public information: Malicious actors can manually search social media profiles and online directories to find publicly available email addresses and personal details. It may also be possible to find someone’s email address if publicly shared content is tied to an email address.
- Web scraping: Spammers use automated tools to scour millions of websites and compile lists of any email addresses they find.
Why you shouldn’t give out your email address
While an email address is often necessary when signing up for online services, it’s best to keep it private. If malicious actors obtain an email address, they can use reverse email search tools to find the owner’s public profiles and learn personal information, which could include the target’s:
- Full name
- Date of birth
- Location
- Phone number
- Employer
- Friends and family
Some email accounts reveal more than others. A Gmail account, for example, links to a Google ID connected to Maps, Drive, YouTube, and other services. If that account is used to publicly share reviews, photos, YouTube content, or files, the email address might be used to find that information.
However, a more likely scenario is that a bad actor would use the email address to obtain information from a data broker or people-search service. Another common method is simply searching the email address to find public information.
What can someone do with your email address without a password?
Here are the most common consequences of an email address getting into the wrong hands.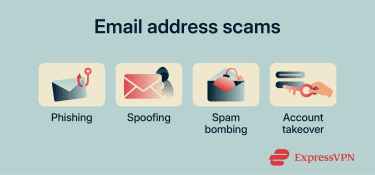
Targeted phishing and social engineering
Scammers can send phishing messages to their target’s email address, designed to trick them into clicking a malicious link, downloading a malicious attachment, or giving away personal data.
Some of these messages are quite convincing, as attackers exploit human emotions. For example, the scammers might pretend to be a trusted company, bank, or someone the target knows.
Many phishing messages make use of threatening, intimidating, or persuasive language to convince the user to take an action. They might claim there is a problem with the target's account and prompt them to log in to fix it, only to redirect them to a fake website and steal their password.
Look-alike emails that trick others
Attackers might also create a fake email address that looks very similar to the target's email address. It might only have slight differences, for example, a “0” instead of an “O.”
Once they’ve set up the fake account, they can use it to contact people the target knows, pretending to be them. Scammers often make up stories to trick these contacts into sending them money or downloading malware onto their devices.
Spam or subscription bombing
Sometimes, attackers use bots to sign a victim’s email address up for hundreds or even thousands of newsletters and subscription services at the same time. As a result, the user gets an influx of unwanted messages.
While this may seem like a mere inconvenience, spam can lay the foundation for a serious attack. Scammers use it to overwhelm the victim while simultaneously carrying out another cyberattack, like an account takeover. The victim may be too preoccupied with spam messages to realize that their account is at risk.
Password reset or account takeover attempts
Attackers can use an email address as a starting point for account takeover attempts. They may run credential stuffing attacks using email and password combinations leaked in data breaches.
They might also gather personal details from the target's social media profiles through open-source intelligence (OSINT) techniques to answer security questions or guess the password.
From there, attackers might manipulate account recovery options or change the password to take control of the account.
Scams, identity theft, or harassment
In some cases, attacks may be more targeted, for example, sending hate mail or other threatening and unwanted messages as a form of stalking or harassment.
If the cybercriminal was able to access enough personal information, they could use it to sign up for services in the target’s name or commit financial fraud. However, it's not usually possible to get the required information from email alone; an attacker would need additional information, like a government ID number or financial information.
How to hide and protect your email address
The first step to staying safe is keeping your email address as private as possible. The fewer websites and services that have access to it, the lower the risk of spam, phishing, and data exposure. The second step is securing your email account so that even if someone obtains your address or attempts to access it, they can’t easily take control of your inbox.
The most effective ways to protect your email address are:
- Using email aliases or masking services: Email masking tools generate unique alias addresses that forward messages to your real inbox. Services like ExpressMailGuard let you sign up for websites without exposing your primary email address, which helps you filter spam and avoid tracking attempts. If an alias starts receiving spam or appears in a data breach, you can disable it without affecting your main account.
- Setting up a “burner” account: A secondary “throwaway” account lets you sign up for sites and services without exposing your main address. It’s best to reserve your main address for trusted contacts and essential services like banking or work.
- Sharing your email selectively: The more sites you enter it into and the more people you share it with, the greater your risk of spam and unwanted messages. Only give it out when necessary.
- Using a strong password: Strong passwords consist of random upper- and lowercase letters, numbers, and symbols, rather than short, easy-to-guess combinations. A secure password manager can help you generate and store passwords.
- Enabling two-factor (2FA) or multi-factor authentication (MFA): Most email providers support 2FA or MFA. With this feature, you’ll have to enter a unique code sent to your device or scan your fingerprint to log in, in addition to providing the password. Even if someone finds out your credentials, they won’t be able to access your inbox.
- Setting up account recovery: Many providers allow account recovery through a backup email address, a phone number, or a recovery code. Setting these up in advance is the fastest way to regain access if the account is ever compromised.
- Watching for suspicious logins and alerts: Many email providers send alerts if they detect suspicious login activity. Additionally, some security tools can notify you if your email address appears on the dark web.
What to do if your email is being misused
If you suspect someone has obtained your email address and is using it without your consent, there are several steps you can take.
Handling unwanted password resets
Unexpected password reset emails are a common sign that someone may be attempting to take over your account. These messages can also be part of a phishing scam, so avoid clicking any links within them. Instead, set a new, strong password, then enable 2FA or MFA.
Dealing with subscription or spam bombing
If you receive a sudden influx of spam or unsolicited subscription confirmation emails, mark them as junk or spam immediately. You can also block the senders or set up filters to automatically divert any further unwanted messages.
Responding to impersonation
You can’t prevent someone from creating a fake account in your name, but you can report it via the platform’s customer support, which may suspend or remove the account. It’s also worth notifying your contacts directly so they know to verify messages that appear to come from you.
FAQ: Common questions about email addresses
What information can someone get from an email address?
What can scammers do with your email?
Can someone hack my bank account with my email address?
Can someone hack your phone through email?
Is it safe to give out your email address?
How can you tell if a scammer is using your email address?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN